Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
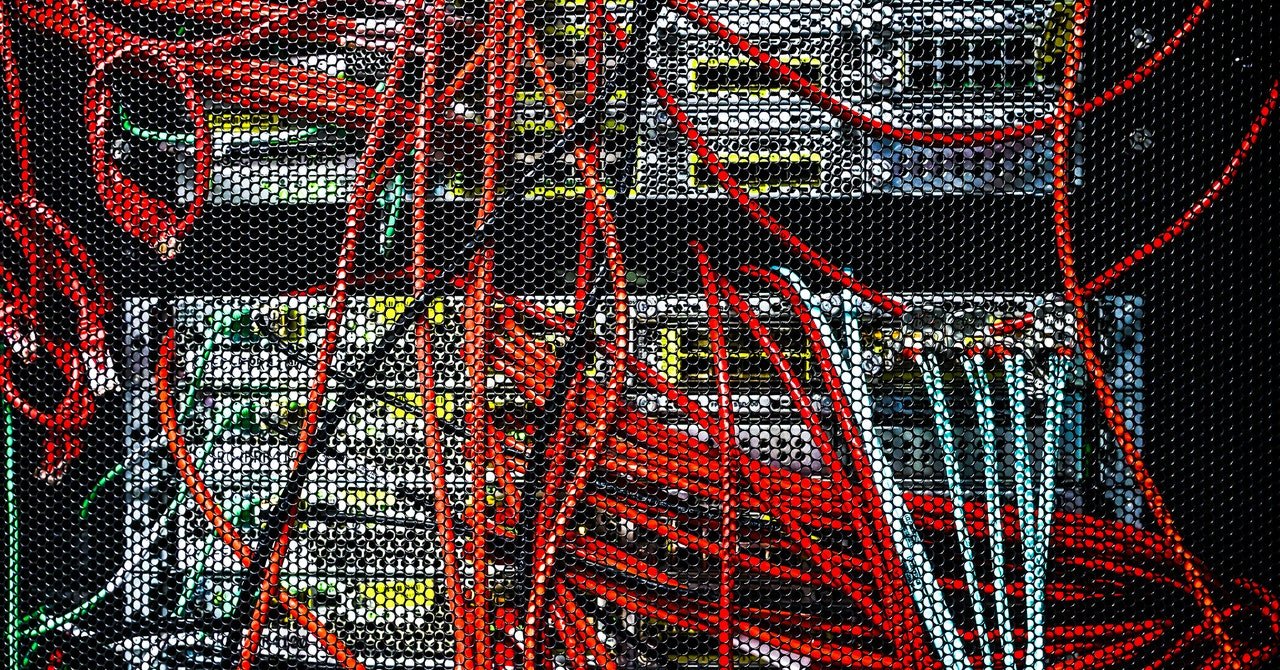
When the Chinese hacker group known as Salt Typhoon was published for the last fall Deeply infiltrated the major telecommunications agencies in the United States-Not less than nine of the phone carrier, and to access the texts of Americans and to violate calls in real time — the US government considered the hacking campaign as a four-alarm fire. Nevertheless, despite the high-profile exposure to these hackers, they have continued their speed of entry into worldwide telecom networks, including more in the United States.
Researchers at the Cybercquire Farm on Wednesday night revealed that they violated five telecom and internet services provided by Salt Typhoons around the world, as well as more than a dozen universities from Utah to Vietnam, from December to January. These telecom include a US Internet service provider and a telecom farm and a telecommunication US -based US -based US -based US -based US -based company, according to agency analysts, though they refused to name their affected wires.
“They are extremely active, and they are going to be extremely active,” Levi Gundart says, who leads the future research team recorded as an Ice Group. “I think there is only a common low-praise for how aggressive they are to turn the telecommunications networks into Swiss cheese.”
To launch this latest campaign of intrusion, Salt typhoon-which is created by Microsoft, has recorded future tracks under his own name Redmike instead of the typhoon handle-the Internet-free web interfaces of the IOS software, which are driven on network, are driven by giant routers and switches. The hackers used two separate weaknesses in the code of those devices, one of which granted primary access and the other provided the main benefits, which often provided full control of strong equipment with the hackers ‘network of victims’ network.
Gundart says, “Anytime you have embedded on communication networks like routers, what you have to access and observe and explode,” Gundart says.
More than 12,000 Cisco devices were found in the recorded future, whose web interfaces were published online, saying that hackers targeted more than a thousand devices installed on worldwide networks. Of these, they seem to be concentrated on a small subsets of telecom and university networks whose Cisco devices they have successfully exploited. For these chosen goals, Salt typhoon hacned censco devices have configured to connect to hackers’ own command-and-control servers through generic routing encapsulation or GRE tunnel — a protocol was used to set up personal communication channels — these connections were used to maintain. Was their access and data steal.
When Wired reached Cisco for comment, the company indicated one Safety suggestion It was published in 2021 on the web interface of his iOS software.
Hacking network applications target victims as entries – often using the known weaknesses that the device owners failed to patches – it has turned into a standard operating manner for salt typhoon and other Chinese hacking groups. This is because these network devices lack many protection control and monitoring software that have been extended to more traditional computing devices such as servers and PCs. Future notes have recorded in his report that sophisticated Chinese spy teams have targeted those weak network applications as the initial intrusion strategy for at least five years.