Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
A dating app, which has declared a cute new wearable this week, is reported to have universally exposed users’ data. Data was granted and private with their approximate locations.
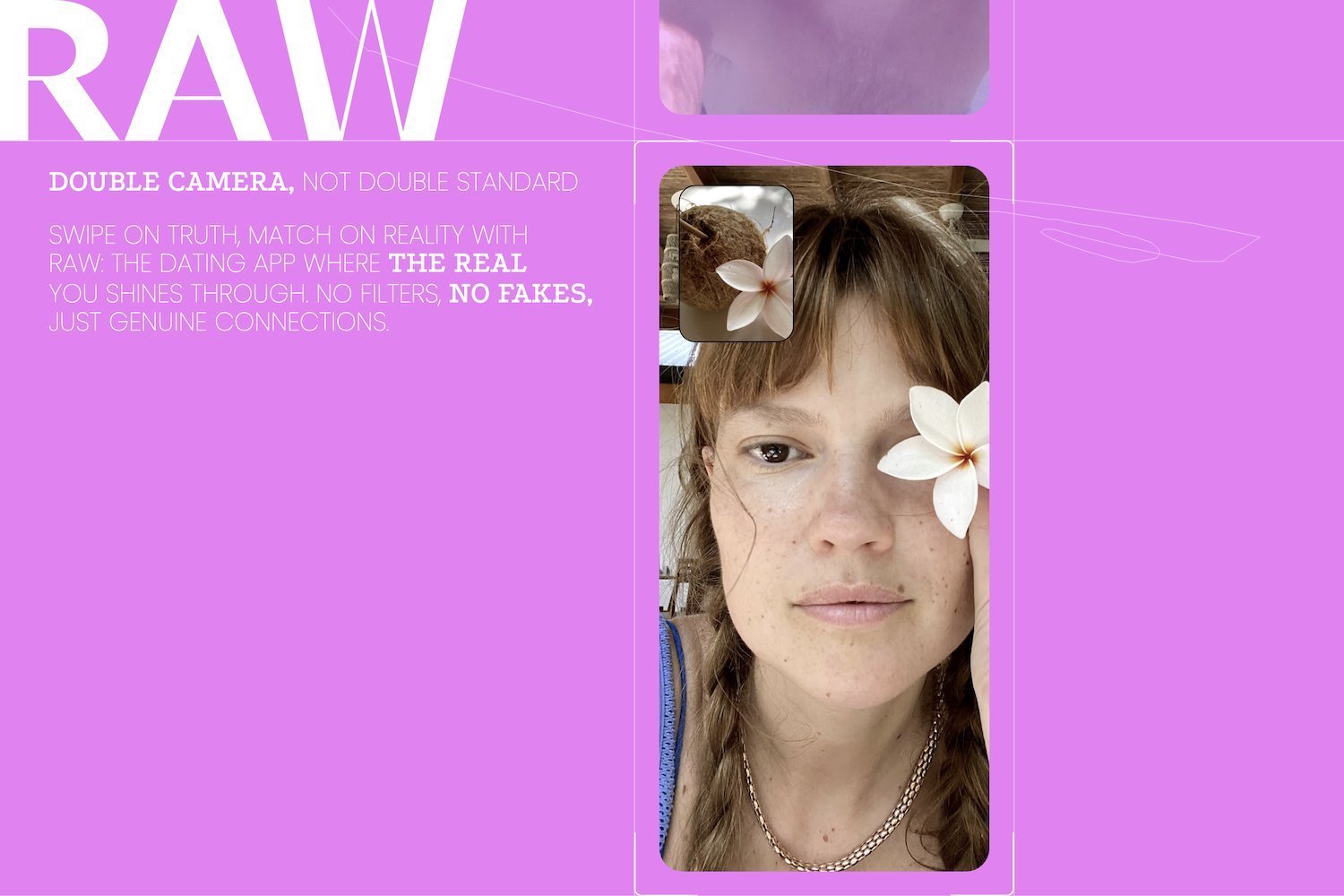
App, raw, say it Promoted Its unique user interface “real and uninterrupted love”, which resembles Berial (It uses the front and rear cameras of your phone) but for dating. Raw recently announced Hardware is a bizarre new pieceIs called Raw ringIn a paragraph allows users to track their lovers’ position so they are not cheating (there is no way that can ever lead to problematic situations, isn’t it?)? Unfortunately, it will appear that the raw is quite a “continuous” fashion promoting something else: users’ data.
TechCrunch Reported that Due to lack of basic digital protection protection, raw accidents kept users’ personal information open to public inspection. In fact, before this week, anyone with web browser was able to access the details app user information with their birth date, display name, sexual choice and data on quite specific “street” position.
TechCrunch says it has discovered the security deficit during a brief examination of the company app. The raw virtualized Android device was downloaded and then TC workers used a network monitoring equipment to monitor the data shipped on the application and from the application. Analysis has shown that personal data was not protected by interrupting any type of authentication. TC says it has discovered the problem in the first “few minutes” of the app to use. TC also noted that although raw users demanded protection with the end-to-end encryption, it was not found any evidence that E2EE was present. They break the protection lufolei:
When we first loaded the app, we could see that the user’s profile information was dragged directly from the organization’s servers, but the server was not protecting the data that returned with any authentication. In practice, it means that anyone can access any other user’s personal information using the web browser to view the exposed server web address –
api.raw.app/users/Another app follows a unique 11-digit number related to the user. Changing the numbers to adjust to the 11-digit identifier of any other user has returned personal information from that user’s profile with their position data. This type of weakness is known as an unsafe direct object reference or iDor, or a type of bug that lets someone else to access or correct data on someone else’s server due to lack of proper security checks in accessing data.
Gizmodo reached raw for more information. According to a statement made on TechCranch, security issues have been patched until Wednesday. “All the last exposed end points have been protected, and we have applied additional security measures to prevent similar problems in the future,” the co-founder of the raw dating app told Marina Anderson Outlet.
It is not uncommon for companies to protect user data badly. It is as strange as it can be heard, the security software industry is not particularly great priority. It can be time -consuming, expensive and slows down other parts of production, so many companies Simply don’t bother with itThe However, with a dating app, however – a business that is dedicated to users’ most intimate (literal) and sensitive data – this is clearly paid to spend some more time to lock stuff. As they say: wrap it before you tap it.