Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
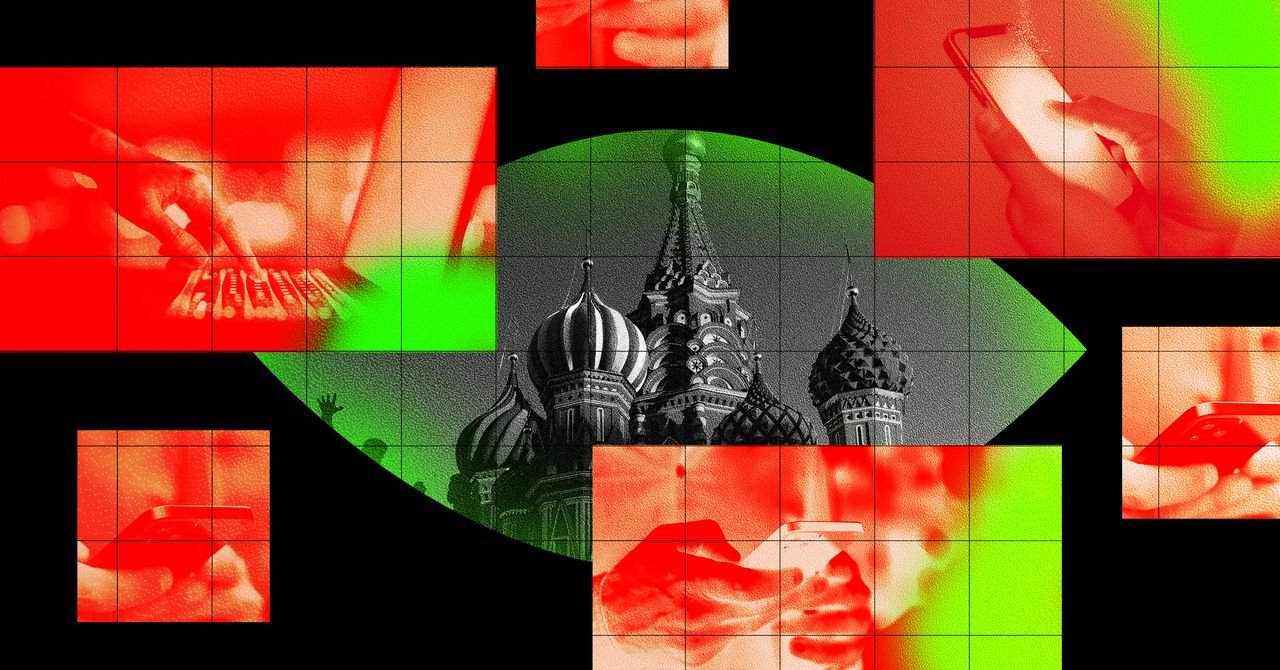
Russian The hacker group known as Turla has performed the most innovative hacking works in the history of Cyberpenzz, To hide their malware contacts on satellite connections Or To extract their own data to hijack the operations of other hackersThe When they are working on the turf of their homes, it appears that if they get more straight, they have made equally significant effort: They seem to have used Russia’s Internet service suppliers to transplant spyware directly to their goals in Moscow.
A Microsoft Protection Research team concentrated on the threat of hacking has released a Report A notorious new spy technique used by Turla is considered to be part of the Kremlin’s FSB intelligence agency. This group, which is also known as Snake, Venomus Beer or Microsoft, is also known as Secret Blizard, has used its state-owned access to the Russian ISPs to install the group’s contaminated software on their PCs with internet traffic and trick victims who work in Moscow. That spyware then disables encryption on those target machines so that they are involuntary on the Internet, their contacts and certificates, such as communications and certificates, are completely at risk of surveillance by the same ISP, and with which state surveillance agencies they cooperate.
Sherode Degrippo, director of Microsoft’s threat intelligence, says the technique represents the rare mixture of the old, more passive approach to the government, where the spy agencies collect the data of ISPS and telecom data and the service. “It blows the boundary between passive surveillance and actual intrusion,” says the degree.
For this particular group of FSB hackers, the degree is added, it also advises a strong new weapon in their arsenal to target anyone within the Russian border. “It is possible to show how they think about Russia -based telecom infrastructure as part of their tool kit,” he said.
According to Microsoft researchers, Turler uses a specific web request browsers when a “Captive Portal” faces, which are commonly used for internet access for internet access to airports, airports or cafes, but also some companies and government agencies inside. On Windows, these captive portals have reached a specific Microsoft website to check if the user’s computer is online. (It is not clear that Turla’s victims used to hack captive portals were actually valid that the target embassies or Turla had somehow pressed on users as part of its hacking technique.)
Some foreign embassy workers were able to redefine Turla goals with the opportunity to control ISPs that connect the Internet so they saw an error message that persuaded them to download an update before accessing the web on their browser’s cryptographic credentials. When an involuntary user agrees, they installed a piece of malware instead that Microsoft calls Apoloshado, which is as disguised as the Caspersky protection update – somewhat involuntarily.
That Apoloshado Malware will then disable the browser’s encryption, sends the computer and quietly removes cryptographic protection for all web data received. Tempering of relatively simple certificates can probably be more difficult to detect than a full -fledged piece of spyware, the degree when achieving the same result.