Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
For this reason, Morgatroid mentions that buyers of Tetra-based radio are free to deploy other solutions for end-to-end encryption on their radio, but he acknowledges that it is widely used as far as we can say by the TCCA. “
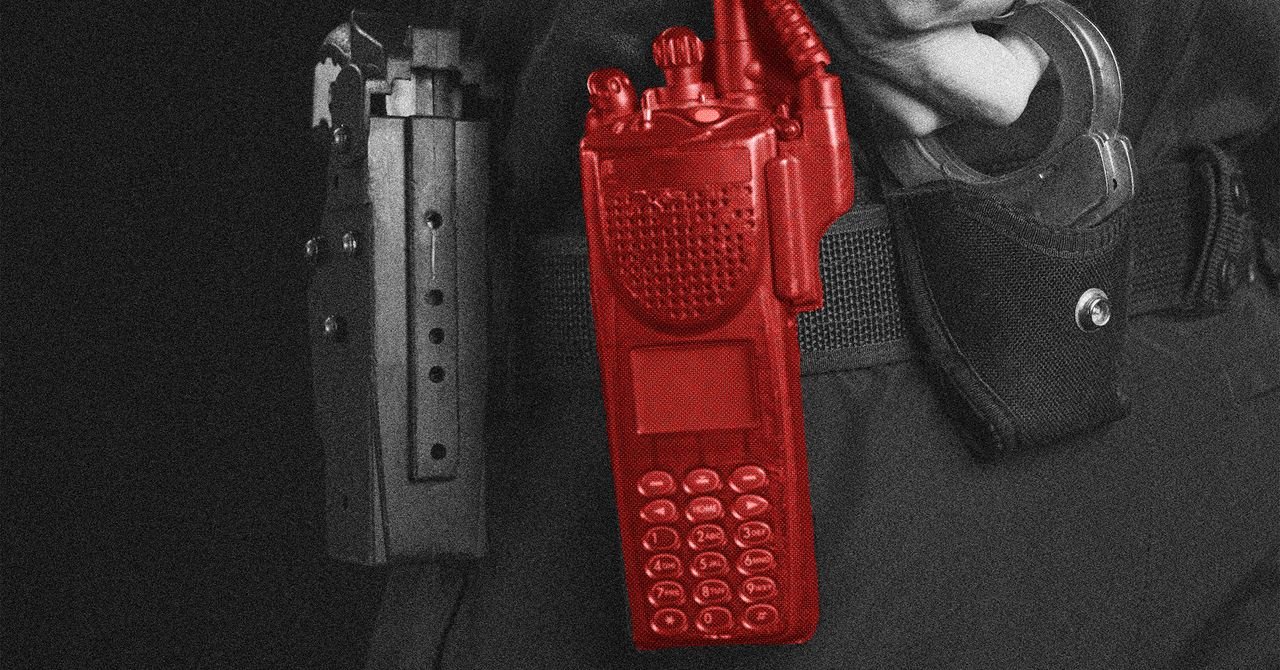
Although tetra -based radio devices are not used by police and military in the United States, most police forces in the world use them. These include police forces in Belgium and Scandinavia countries, as well as Serbia, Moldova, Bulgaria and Massadonia and Iran, Iraq, Lebanon and Syria in the Middle East of Syria. Defense ministries in Bulgaria, Kazakhstan and Syria also use them, such as Polish military protective agencies, Finnish Defense Force and Lebanon and Saudi Arabia’s intelligence services. This is not clear, but some of them also set up decryption with their radios.
There are four encryption algorithms in the Tetra Standard – TA 1, TE2, TE3 and T4 – which can use radio manufacturers on various products depending on intended customers and usage. There are various levels of algorithm protection based on whether radios will be sold in or outside Europe. For example, T2 is limited to use in radios used by Europe’s police, emergency services, military and intelligence agencies. T3 available for police and emergency services radios used outside Europe but only in countries considered “friendly” in the EU. In countries considered not friendly for Europe like Iran, only tea is available for the radio used by the Public Safety Agency, the police agency and the military. However, it is also used in critical infrastructure for machine-to-machine communication in industrial control settings like pipelines, railways and electric grids in the United States and other countries.
Four tetra encryption uses the 80-bit key to secure contact algorithm. However, Dutch researchers revealed in 2021 that T1 has a feature that its key can only reduce 32 bits, which researchers allow it to crack in less than a minute.
In the case of E2EE, researchers have discovered that the implementation that they have tested begins with a key that is more secure than used in tetra algorithms, but it becomes 56 bit, which is probably allowing someone to decryep the voice and data communication. They also found a second weakness that lets someone send fraud messages or re -play the valids so that using radios to spread misinformation or confusion among the staff.
Researchers say that voice traffic injections and the ability to re-play messages affect all users of the TCCA from the end to the end encryption scheme. They say that this is the result of the error of TCCA E2 EE protocol design instead of a specific implementation. They also say that “law enforcement last users” confirmed to them that this error is on radio produced by vendors other than Seapura.
However, researchers say that a subset of only from the end to the end encryption is probably affected by the decreased weakness as it depends on how encryption was applied to radios sold in different countries.