Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
This is the new search The week showed that A wrong configured platform used by the Homeland Security section Left sensitive National Protection Information – EXPOSED AND ACCESSIVE to thousands of people – including Americans’ surveillance data. Meanwhile, 5 officers in New York Immigration and customs enforcement and New York Police Department were arrested in this week or about 26 federal plaza– The unhealthy situation where the ice court has given people to the judgment is an unhealthy situation.
Russia operated clearly Military practice testing hypersonic missile Near the NATO border, Kremlin has already spread tension in the region after the drone was blown up in the Polish and Romanian airspace. Scammers have one New Equipment for SPAM text transmitting, known as “SMS Blasters”“It can send 100,000 texts per hour to avoid the anti-spam measures of the telecom company. Scammers deploy repressed cell towers to drive people to connect with rogue devices so they can send direct texts and bypass filters. Virtually all azur can be used for access to customer accountsA potential disaster.
Wired Burner’s Detailed Guide This Week To Achieve and Use Burner PhoneAs well as alternatives that are more personal than regular phones but not like a real burner. And we’ve updated to us The best VPNS guide
But wait, there is more! Every week, we look at the news of protection and privacy we didn’t cover the ourselves deeply. Click the titles to read the whole stories. And stay safe there.
The Cyber Security World has seen the World, in its growing frustration, in great extent Software supply chain attacksIn which the hackers hide their code into the legitimate piece of software so that it uses the code around the world silently on every system. In recent years, hackers have even tried to connect A software supply chain attack is another oneFinding the second software developer goal among their victims to compromise with another part of the software to compromise and turn on a new round of infection. This week saw a new and worrying evolution of those techniques: a full-fledged self-deployed supply chain attack worm.
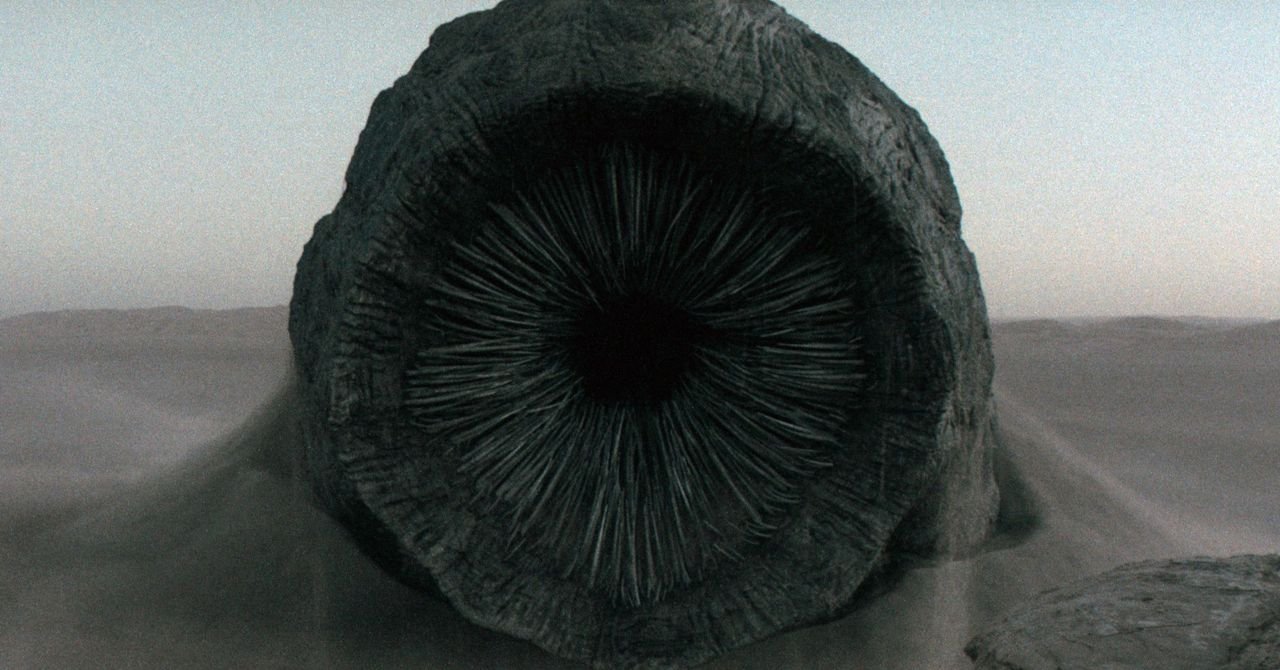
Shay-Hulud is dubbed after the name of the Freman of the Rakshasi Sandworms in the Cy-Fi novel. Unemployed (And the name of the Github page where the malware has published theft credentials of the victims) Code used by developers of JavaScript has compromised on several hundred open-source software packages on Node packets or NPM. Shay-Hulud worms are designed to infect a system that uses one of those software packages, then hunts for more NPM credentials on that system so that it can pollute the other software package and continue its spread.
By a count, worms have spread More than 180 software packagesCybercuity firm, including 25 used by Crowdstrike, though Crowdstrick has since removed their NPM from the NPM storage. Another calculation of the Cybercquirement Farm keeps the reversinglabs the calculation even higher More than 700 affected code packagesThe It makes Shai-Hulud one of the largest supply chain attacks in history, although its mass credentials are far from the intention of stealing the certificate.
Western privacy as expected distopia as expected distopia as the technology industry and government data collection has not been checked for the Chinese surveillance system for China for a long time. However, in a broad Associated Press investigation, China’s surveillance systems highlighting how the US technology was originally created. AP journalists found that Beijing officials from the “Golden Shield” policing system -“Golden Shield” policing system and used the alleged terrorists to make the accused terrorists crack on the equipment used to create Yuhrs, Dee, Dell, IIP, Co -, IIP and cracking on the cracked terror, and mud. Services, Western Digital and HP. In many cases, the AP found the Chinese language marketing materials where Western companies, especially Chinese police and domestic intelligence services, provide surveillance applications and equipment.
Originally a rare hacking and extortion cyber criminal gang based in Western countries, spider spider has published a trail of chaos across the Internet over the years, the target of the United Kingdom Marx and Spencer Mudi chains from the MGM Resorts and Caesar’s palace. Now two of the notorious groups of the notorious group have been arrested in the UK: 3-year-old Thalaha Jubair and 3-year-old Ovens Flower, both accused of hacking transport for London transit system-have been more than $ 1 million in many targets. Jubair alone has been accused of infiltrating 47 companies. The arrests are the latest in a string of the boost at the spider -spider, which still continues to violate the violation almost continuously. Noah Urban, who was convicted of the scattered spiders’ allegations related to the activities of the spider, he spoke to Bloomberg Business Week from jail Long profile of his cyber criminal carrierThe The 26 -year -old Urban has been sentenced to a decade.