Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
For all apps to spread the beans about who you are dating with, it is satirical that the Tionahar was spreading the personal information of thousands of its users on the open web.
Tionhar was designed to share photos and information about the women who claimed to have dated for men. However a lot of choice Tea, dating-gossip app for women It was trying to replicate, the toion was the holes in the protection of the tion, which revealed their users’ personal information, including their driver’s license and other government-jerie identity documents, e.g. TechCrunch has reported Last week.
Applications like this gated community were clearly created to share information about their relationship under the personal protection of users. However, schedule coding and security defects highlight the risk of underlying privacy in need to submit sensitive information for users’ applications and websites.
Such risks are simply going to get worse; There are already popular applications and web services Adhere to the Age Verification Act That needs people Submit their identity documents Before the database of human personal information is the privacy and security risk related to conservation before they allow access to adult-them of themselves.
When TechCrunch published our story last week, we did not disclose the specific details of the bugs we discovered in the tion, making a cautiously mistake so that the bad actors did not help use the bug. Instead of, We decided to reveal a limited manifestationDue to the rising popularity of the app and the use of the app when using the app that immediately faced the risk.
As a time of publication, the Apple App Store’s Free App Chart was Tionahar #2, it is still a position placed by the app.
The flaws we received seem to have been resolved. TechCrunch can now share that in 10 minutes of sending a link to the App Store app, we have been able to find the user’s driver’s license, easy thanks for finding errors in the app’s public-facing backward system or API.
Developer of the application, Javier Lampkin, we did not respond to multiple requests for commenting after submitting the details of the security defects, nor promise to inform the state controllers of the damaged tion users or protection coating.
We also asked Lampkin whether any security was reviewed before the Tionahar app was launched, but we didn’t get any reply. (There is something more about the publication of us after))
Ok, start watching.
Even before we download the app, we first wanted to know where the Tionahar was hosted on the Internet by seeing its public infrastructure such as websites and its domain.
This is usually a good place to start because it helps understand what the domain is connected to the Internet.
To find the name of the domain, we first saw (at the opportunity) Apple App Store List in App Store To find the app’s website. It is usually found in its privacy policy, apps must include Apple before listing them. (Application list also claimed that the developer was “not collecting any data from this app”, which is displayed in display, so accept as much as you do))
The Tioner’s Privacy Policy was in the form of a published Google Dock, it included an email address with a teaonher.com Domain, but there is no website.
The website was not universal at that time, so without loading a website, we saw the domain public-facing DNS records, which could help detect what the hosted in the domain, such as the type of email server or web hosting. We also wanted to find any public subdomains that could use to host functionality for the developer application (or hosts other resources which Perhaps not to be universal), Such as admin dashboard, database or other web-facing service.
But when we looked at the public internet records of the tion, it had no meaningful information other than its single subdomain, appserver.teaonher.comThe
When we opened this page in our browser, what was the landing page for Tion’s API (for curiosity, We’ve uploaded a copy here) An API simply allows things to communicate with each other on the Internet, such as an application connects to its central database.
It was on this landing page that we received the open email address and plaintext password (which “Password” was not too far away) To access the Tionahar “Admin Panel” for Lampkin’s account.
The API page shows that the admin panel used to manage the document verification system and user was located in “Localhost”, which simply refers to the physical computer run and it may not be directly accessible from the Internet. It is not clear whether anyone could use credentials to access the admin panel, but it was a very worrying search itself.
At the moment, we had about two minutes.
Otherwise, the API Landing Page did nothing more than to indicate what API could do. A number of API endpoints are listed on the page, which will need to be accessed to work, such as recovering users’ records from the database of the tion, to release users reviews and send notifications.
With the knowledge of these last points, it can be easier to interact directly with the API, so that we are imitating the app itself. Each API is different, so it can take time to determine how an API works and how to contact one’s, such as what end points to use and the parameters needed to speak the language effectively. Applications such as postman may be helpful in accessing and interacting directly with APIs but APIs should not be done when it should be done and requires a specific degree test and error (and patience) to create data spit.
However, in this case, there was easier ways.
This includes the API Landing page Called a last point /docsIt has auto-exposed documentation of the API (powered by a product called Swagar UI) that has a full list of commands that can be performed in the API.
This documentation page was effectively a master sheet of all activities that you can perform as a regular application user and more importantly, creating new user as the app administrator, verifying users’ identity documents, modifying comments and more.
The API documentation is also featured to ask the Tioner API and return the user’s data, basically to recover data from the backnd server of our app and to display it in the browser.
Although developers are not unusual to publish their API documentation, the problem here was that some API requests can be done without any authentication – no password or certificate was needed to refund the information from the tion database. In other words, you can run commands in API to access users’ personal data that should not be accessible to any user of the app, leave someone on the Internet.
All of this was efficiently and publicly enrolled to see anyone.
For example, asking for a list of users in the Identity Verification Qatar, for example – there is nothing but pressing a button on the API page, nothing is fancy here – recently a few dozen account records for people signed up to tionhar will return.
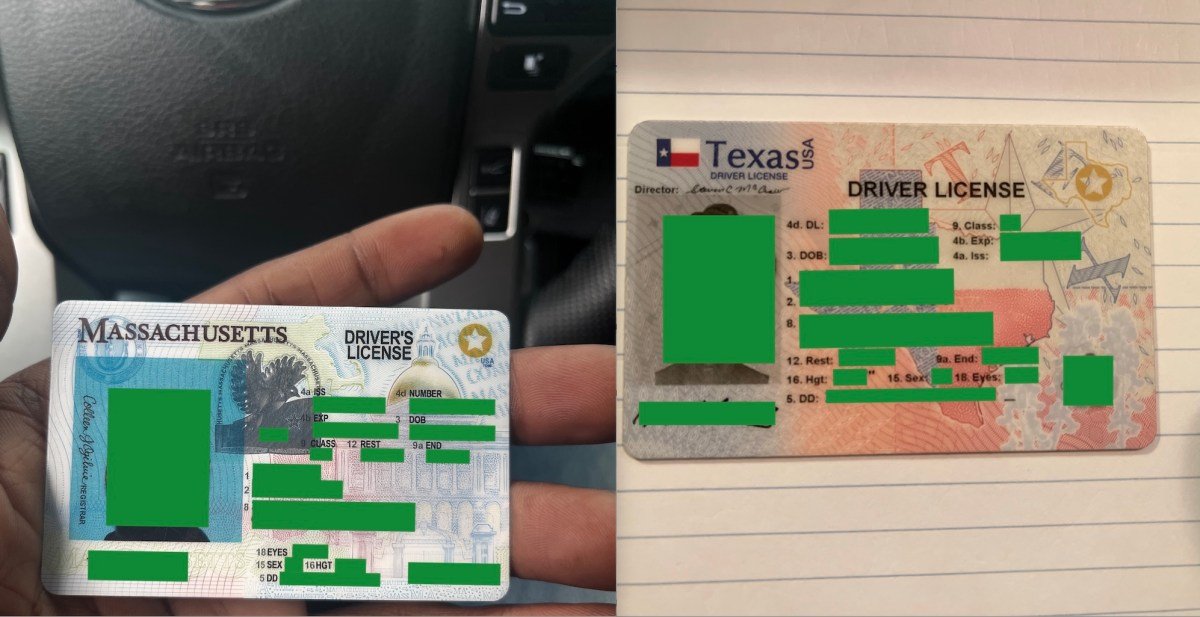
Applications in the records that return from the server are unique identifier (mainly a string of random letters and numbers), their public profile screen names and self-dedicated age and location, including their personal email address. Records also included the web address link containing the driver’s license and photos of the related selfies.
The worst thing is, these photos of the driver’s license, official-giri ID and selfie were stored on an Amazon-Hosted S3 cloud server set as universally accessible to anyone with their web addresses. This public setting allows someone to open files without any restrictions on someone who’s identity documents.

With that unique user identifier, we can also use the API page to directly find the records of separate users, which return their account data and any related identity documents. With seamless access to API, a malicious user could scrape a lot of user data from the app, much like what happened Tea app for startingThe
From the bean to the cup, it was about 10 minutes and we haven’t logged in the app yet. The bugs were so easy that it would be free fate if no one found them polluted before us.
We have asked, but do not say lampkin to determine if anyone has a technical skill like logs to determine whether the API has used (or abuse) to obtain access to the verification documents of users by scraping the web addresses from API.
Since our report to Lampkin, the API Landing Page has been dropped with its documentation page and now it only shows the state of the server that is going on as Tioer API “Healthy”. At least in the cursory examination, the API now seems to depend on authentication and previous calls made using API no longer work.
Users uploaded identity documents are also limited to public views.
During our inquiry, the teoner had no official website, provided with the Email address listed in the Privacy Policy in an attempt to publish TechCrunch Protection Laps.
However, the email comes back with an error as the email address is not found. We have tried to contact Lampkin via email address on his website Newville media, but our email came back with the same error message.
TechCrunch reached the Lampkin via the Linch LinkedIn message, asking him to provide an email address where we could send details of security errors. The lampkin responded with a general “support” email address in the response.
When TechCrunch reveals a security error, we first reached to confirm that any person or company is the right recipient. Otherwise, blindly the wrong person can create the risk of sending the details of the protection bug. Before sharing the specific details of the errors, we have asked the recipient of the “support” email address if it was the correct address for publishing any security exposure involving the Tionhar user data.
Lampkin replied, “You must confuse us with ‘The Tea App’. (We had no protection violation or data were leaked,” he said. (It did.) “We have some bots but we still have no big scales in that conversation, sorry you were sorry.”
Satisfied that we have made contact with the right person (though not with the reactions we received), sharing details of TechCrunch Protection Error, as well as a copy of Lampkin’s own data to underoscore several links for open driver’s license and the severity of security issues.
“Thank you for this information. It’s very related. We’re going to jump to it right now,” said Lampkin.
Despite several follow-up emails, we have not heard from Lampkin since we released security defects.
You do not come to a person’s software shop or something it goes A billionaire siblings coding on a weekend: Developers still have a responsibility to protect their users’ data. If you can’t keep your users’ personal data secure, don’t make it to start it.
If you have evidence of a popular application or service leak or information publishing, please contact. You can safely contact this reporter through an encrypted message on Jacheitker.1337 in the signal.